Search interest around thejavasea.me leaks aio-tlp370 has grown because people want clarity. When technical dataset names begin circulating online, they often sound more alarming than they actually are—or sometimes less alarming than they should be. The difficulty is knowing which situation applies.
In this case, AIO-TLP370 appears to refer to a compiled exposure archive rather than a single confirmed intrusion affecting a single organization. That difference matters. Aggregated datasets can still pose real risks, especially when reused credentials or configuration details are included.
Understanding what the label means helps separate speculation from practical security advice.
Table of Contents
What is thejavasea.me Leaks AIO-TLP370?
The name itself gives useful clues once broken into parts.
Security communities often use shorthand identifiers when discussing compiled breach material. In this case:
- AIO usually means “all-in-one.”
- TLP refers to the Traffic Light Protocol classification system
- 370 likely indicates a dataset version reference
Taken together, the label suggests a structured bundle assembled from multiple exposure sources rather than a newly discovered attack targeting a single service.
That distinction is important because aggregated archives behave differently from traditional breach incidents.
What Kind of Data Was Reportedly Included in AIO-TLP370?
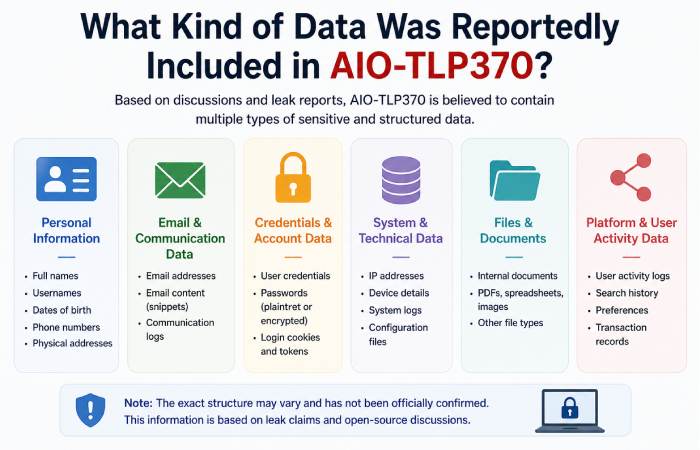
Descriptions of datasets with similar naming patterns typically mention mixed technical material collected from earlier exposures.
Examples often include:
email address lists
password combinations
API credentials
configuration fragments
development environment references
Not every compiled archive contains all of these elements. However, the goal of an “all-in-one” dataset is usually consolidation rather than originality. It gathers material already circulating elsewhere and makes it searchable in one place.
That convenience increases its usefulness to attackers.
Why Aggregated Leak Packages Can Be More Risky Than Single Breaches
When people hear about a breach, they usually imagine one service being compromised.
Aggregated exposure bundles change the situation.
Instead of affecting one system at a time, they allow attackers to cross-reference multiple incidents simultaneously. That makes it easier to identify patterns such as:
reused passwords
shared usernames
linked email identities
exposed integration credentials
These connections are what make compilation datasets valuable to attackers—even when the underlying material is not new.
Was thejavasea.me Leaks AIO-TLP370 a Confirmed Cybersecurity Incident?
Public reporting around AIO-style archives often begins in research communities rather than through official disclosure statements.
That means:
The dataset may include older exposure material
It may combine unrelated breach sources
It may circulate mainly among analysts
It may not represent a new compromise event
Security teams sometimes review such datasets proactively just to confirm whether internal references appear inside them.
So the presence of an archive name online does not automatically indicate a new breach.
What the Traffic Light Protocol (TLP) Means in Cybersecurity
The Traffic Light Protocol is a classification method used by security professionals to control the spread of sensitive information.
It does not measure the danger level. Instead, it describes sharing boundaries.
Typical categories include:
TLP Red — restricted sharing
TLP Amber — limited organizational sharing
TLP Green — community sharing allowed
TLP White — public distribution permitted
When the label appears in dataset names, it usually reflects handling expectations rather than severity.
Why thejavasea.me Became Linked With Dataset Discussions
Platforms sometimes become associated with exposure archives simply because conversations about them happen there.
In technical communities, this can occur when:
forumsanalyzee dataset structure
Researchers compare archive versions
security enthusiasts exchange indicators
documentation appears alongside related material
Association alone does not confirm origin. It often reflects where the discussion took place rather than where the dataset was created.
Cybersecurity Risks Linked to AIO-TLP370-Style Datasets
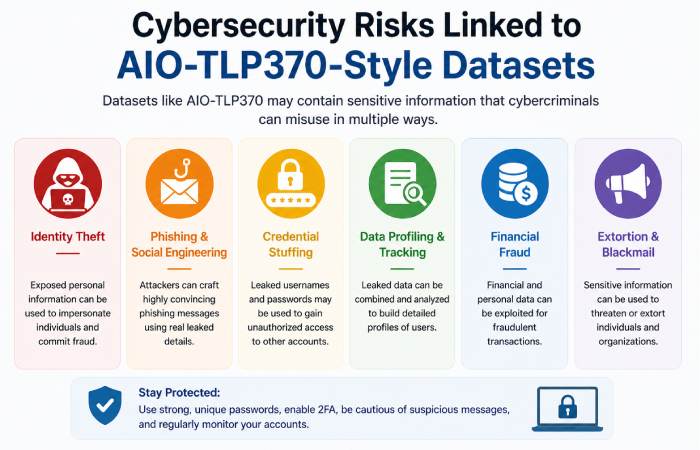
Aggregated exposure archives can create several types of downstream risk.
These include:
credential-stuffing attempts
API token misuse
phishing campaign targeting
cloud resource probing
Even when the underlying data comes from older incidents, packaging it together increases its practical usability.
Could Personal Users Be Affected?
For individual users, the biggest factor is password reuse.
Someone using unique credentials across services is far less likely to experience follow-on compromise from compiled datasets.
Risk increases when:
The same password appears on multiple sites
accounts share recovery email addresses
Authentication relies on weak security questions
Multi-factor authentication reduces exposure significantly in these scenarios.
How Organizations May Be Impacted
Organizations face a different type of exposure risk.
Configuration fragments or integration references can sometimes help attackers understand infrastructure layout more quickly. Even partial visibility into system relationships can improve the efficiency of attack planning.
Typical concerns include:
service-dependency mapping
credential reuse across integrations
exposed development references
legacy configuration visibility
Because modern software ecosystems are interconnected, small fragments can still provide context.
Is Accessing Leak Archives Like AIO-TLP370 Legal?
Many readers ask this question directly.
In the United States and many other jurisdictions, downloading or redistributing unauthorized exposure datasets can create legal risk—especially when credentials or proprietary material are involved.
Security researchers operate within structured legal and ethical frameworks when analyzing such archives. General users should avoid attempting to access them directly.
Monitoring exposure through legitimate services is the safer approach.
How to Check Whether Your Data Was Included in Exposure Datasets
Instead of searching unofficial archives, safer steps include:
checking recognized breach-monitoring platforms
changing reused passwords immediately
enabling multi-factor authentication
watching for suspicious login alerts
These steps remain effective regardless of the dataset’s origin.
Immediate Security Steps to Take After Hearing About Data Leak Reports
Even when exposure is uncertain, taking preventive action helps.
Practical responses include:
updating passwords on important accounts
activating multi-factor authentication
reviewing saved browser credentials
monitoring financial statements
updating installed software
These steps reduce risk across multiple scenarios, not just this one.
How AIO-Style Exposure Packages Affect the Software Supply Chain
Compiled datasets sometimes include technical references that relate to development environments rather than personal accounts.
Possible implications include:
dependency credential exposure
integration-token reuse risks
vendor-relationship visibility
cloud configuration references
Because modern applications rely heavily on shared infrastructure components, even indirect exposure can matter.
AIO-TLP370 vs Later Dataset Variants
Sequential dataset numbers usually reflect iteration rather than escalation.
For example:
| Dataset | Typical Interpretation |
| AIO-TLP370 | earlier compiled reference archive |
| AIO-TLP371 | expanded follow-on dataset version |
Version numbering alone does not indicate a change in severity.
How Credential-Stuffing Attacks Work
Credential-stuffing attacks rely on one assumption: people reuse passwords.
Attackers take leaked login combinations and test them automatically across multiple services. If credentials match elsewhere, accounts may be accessed without needing additional technical exploits.
This is why password uniqueness remains one of the strongest security protections available to individuals.
What an API Key Leak Means for Developers
API keys allow applications to communicate securely.
If exposed publicly, they can sometimes allow attackers to:
access services
consume paid resources
interact with infrastructure
retrieve sensitive data
Rotating keys quickly after suspected exposure is standard practice.
How Companies Typically Respond to Source-Code Exposure Concerns
When configuration fragments or repository references appear inside compiled datasets, organizations usually respond methodically.
Common actions include:
credential rotation
access-token revocation
dependency audits
monitoring unusual activity
reviewing infrastructure access paths
These steps help reduce secondary risk even when exposure remains uncertain.
Best Free Tools to Monitor Data-Exposure Alerts
Several legitimate monitoring tools help users stay informed safely.
Examples include:
Have I Been Pwned
browser-based password monitors
identity-alert notifications
email exposure tracking services
Using recognized monitoring platforms is safer than manually locating exposure datasets.
How to Protect Yourself From Future Credential Leak Packages
Good security habits remain the most reliable protection.
Recommended steps include:
using password managers
creating unique credentials per service
enabling multi-factor authentication
monitoring account activity regularly
These practices reduce exposure impact regardless of the dataset name involved.
Frequently Asked Questions About thejavasea.me Leaks AIO-TLP370
What is thejavasea.me leaks AIO-TLP370?
It appears to describe a compiled exposure archive built from multiple credential sources rather than a single breach.
Does it affect everyday users?
Only if reused credentials appeared in the underlying exposure material.
Is it safe to download leak archives?
No. Accessing unauthorized datasets can create legal and security risks.
Should passwords be changed after hearing about it?
Yes—especially if the same password is used across multiple services.
Final Thoughts on thejavasea.me Leaks AIO-TLP370 Incident
Thejavasea.me leaks AIO-TLP370, highlighting how compiled exposure archives can extend the impact of earlier breaches by combining scattered material into a single searchable dataset. While individual risk depends largely on credential reuse habits, updating passwords, enabling multi-factor authentication, and monitoring exposure alerts remain the most effective defensive steps available.

